5210R/5211R: Two-Factor-Auth (2FA)
Two-Factor-Auth (2FA) protection for SSH has been added to BlueOnyx 5211R and 5210R.
Two-Factor-Auth (2FA) is now available for BlueOnyx 5211R and BlueOnyx 5210R. Our implementation of 2FA adds an additional layer of security to SSH enabled Shell accounts. If an account as Shell enabled and 2FA enabled, then during login the user will be asked for the username, the password and additionally a one-time-use "Verification Code" that you can generate in a 2FA application on your mobile device. Supported 2FA authenticator applications are the Google Authenticator and the RedHat FreeOTP app, which are both available for Android and Apple devices. Download links for these apps are below.
Authenticator usage:
- Download the Google Authenticator or the RedHat FreeOTP Authenticator app from the Apple App Store or Google Play Store.
- Open the app and tap the "+" button to add a new account.
- Select "Scan barcode" and on the BlueOnyx GUI page "Personal Profile" / "SSH Access" scan the QR code "2FA QR-image" or enter the "Authentication Key" manually.
- When logging in to the BlueOnyx server via SSH enter your username and password as well as the verification code generated by the Authenticator app.
- To ensure the security of your account, do not share your key or one-time codes with anyone.
Authenticator App Download Links:
|
Google Authenticator: |
RedHat FreeOTP Authenticator: |
|
 |
 |
|
 |
 |
GUI Integration in BlueOnyx
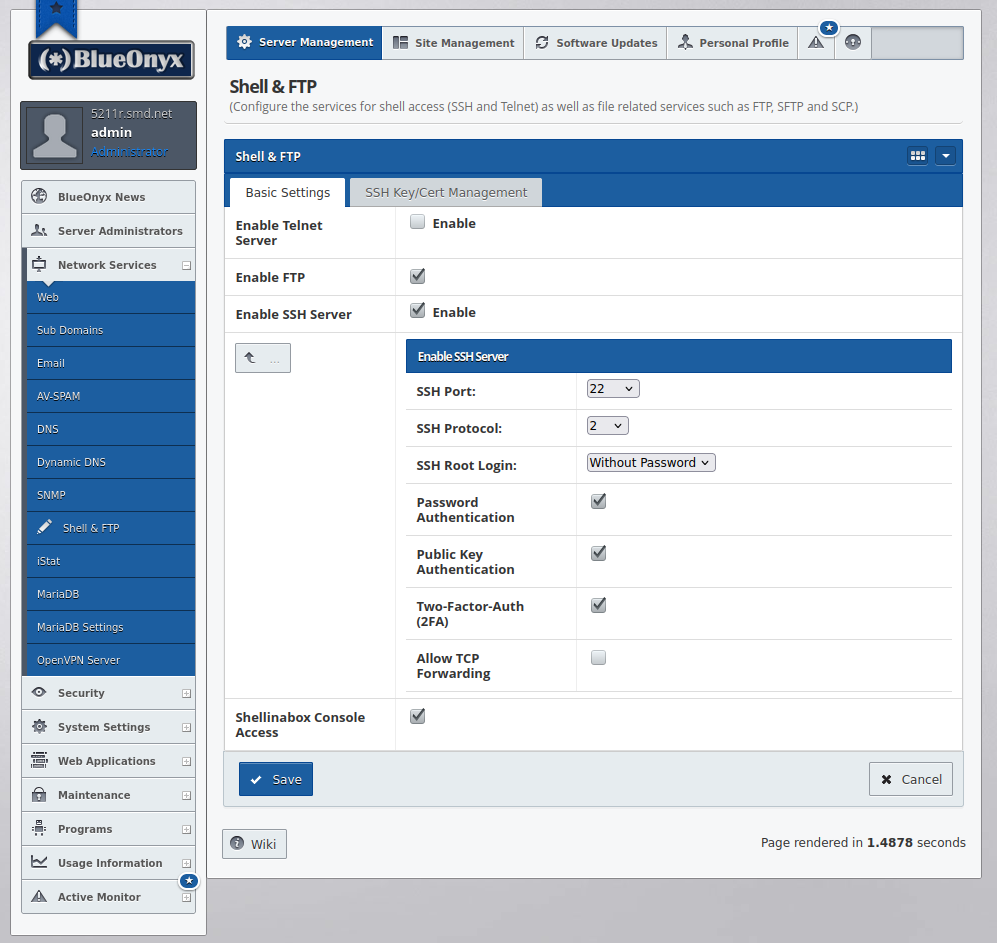
The server administrator needs to enable "Two-Factor-Auth (2FA)" under "Server Management" / "Network Services" / "Shell & FTP". Please note that you may turn off "Password Authentication" and leave "Public Key Authentication" ticked. The way our 2FA integration works is this:
If a user has SSH keys exchanged, he can still login without password AND without 2FA. We consider exchanged SSH keys secure enough.
If a user doesn't have SSH keys exchanged, but has Shell access and has 2FA enabled? Regardless if "Password Authentication" is on or off: He will receive a username and password prompt and also the prompt to enter his 2FA key generated in the 2FA authenticator app.
If a user has Shell, 2FA is disabled for him and SSH is configured without "Password Authentication"? In that case login is only possible via exchanged SSH keys.
This way key exchange still works as before and 2FA can be used if a user doesn't have SSH keys exchanged yet.
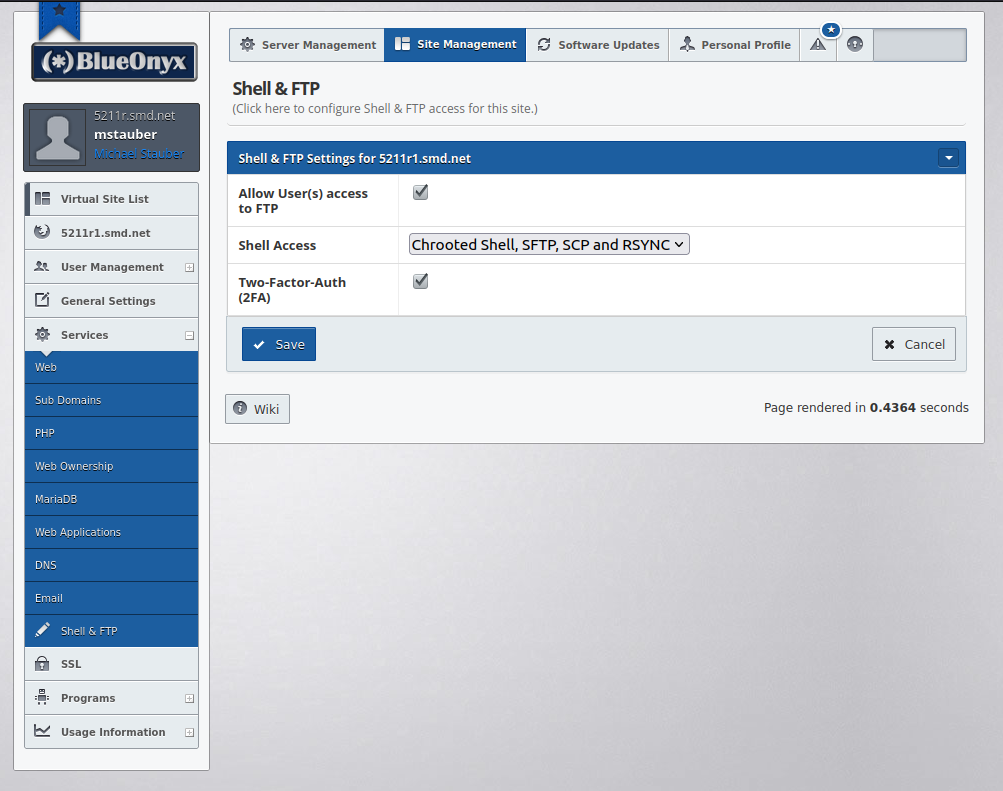
2FA Vsite integration
Each Vsite can have 2FA enabled or disabled for its users as shown below.
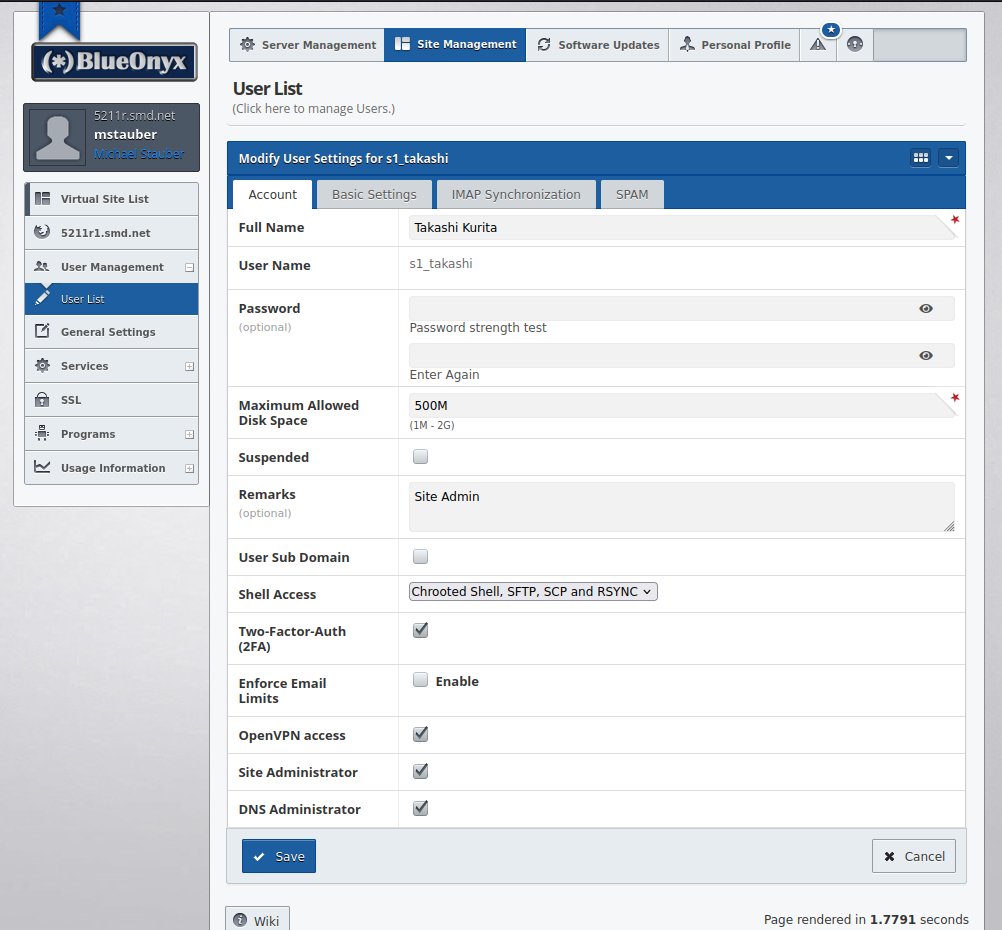
2FA User Management Integration
If a Vsite has 2FA enabled, each of its users with some form of Shell access active automatically gets 2FA activated.
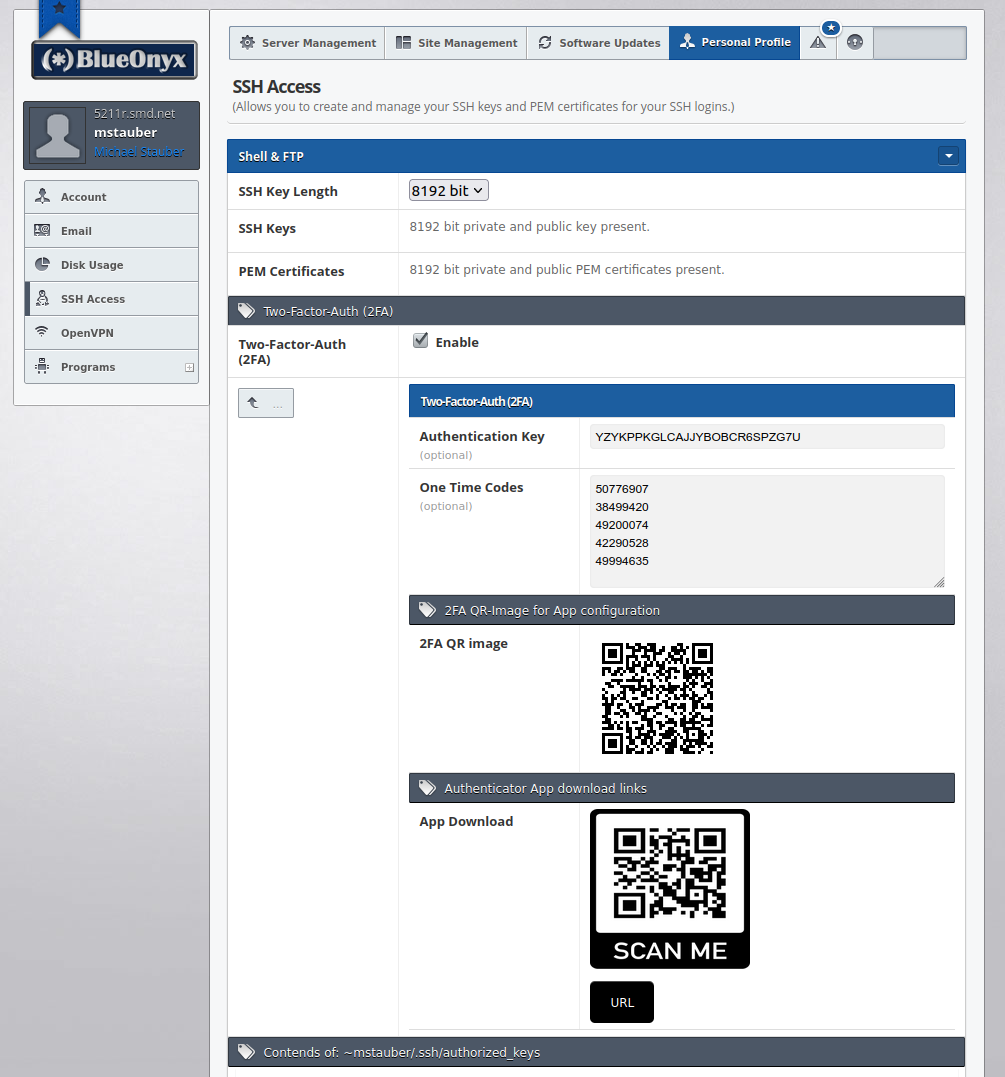
2FA Credentials for Users
Each user with enabled 2FA can find his or her own 2FA credentials in the GUI under "Personal Profile" / "SSH Access" as shown above. The "Authentication Key" can be used to manually configure an authenticator app, but the easiest way is by scanning the QR code with the authenticator application.
The "One Time Codes" shown on this GUI page can each be used once in case access to the authenticator application is not possible.
The "2FA QR image" is really all one typically needs. Open your 2FA application on your mobile device. This should either be the Google Authenticator app or the RedHat FreeOTP authenticator app. Click on the '+' button in the app to add an account, then click the QR icon in the app and point the camera of your mobile device to this QR-image. That will automatically configure your 2FA app with the details of this SSH account in order to provide 2FA one-time-codes, which you can then use during SSH logins.
This GUI page also another QR-image called "App Download". If scanned in a QR code reader (or by clicking on the "URL"-button instead) this page will open and the user can install the 2FA app of his choice by following the links to the respective appstore matching his device architecture.
2FA for other BlueOnyx versions
We are considering to port this to BlueOnyx 5209R as well, but we don't have a time table for that yet.