Modern 2FA Implementation
The BlueOnyx 2FA implementation is getting an overhaul.
Two years ago we added MFA/2FA protection for SSH and GUI logins to BlueOnyx. This has served us well, but the overall integration of it was perhaps somewhat suboptimal. After long and hard look at what we had we decided: We can do better.
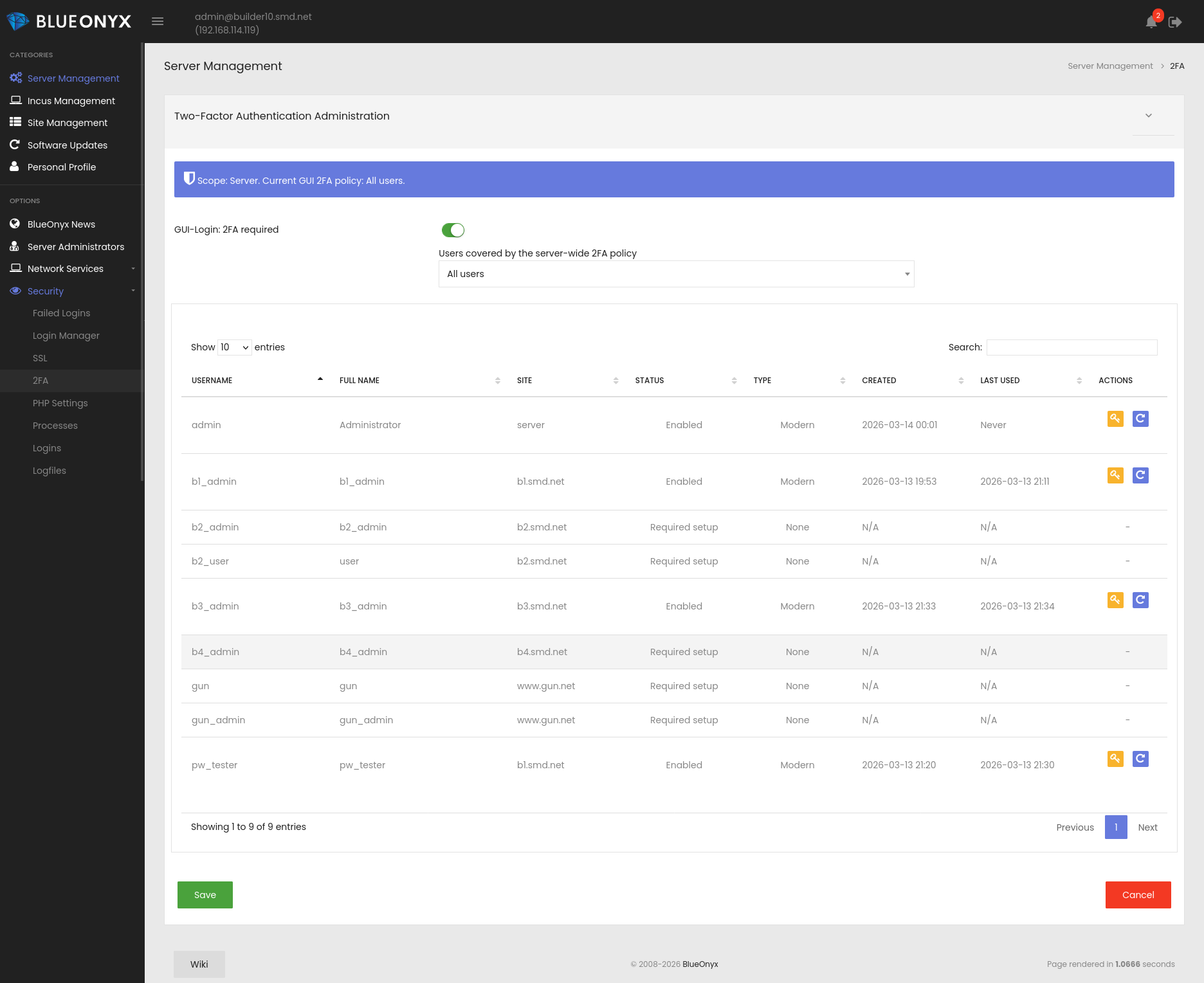
The updated implementation brings 2FA management into a single, central location and makes setup much clearer for both administrators and end users. Server administrators can now define GUI 2FA policy centrally:
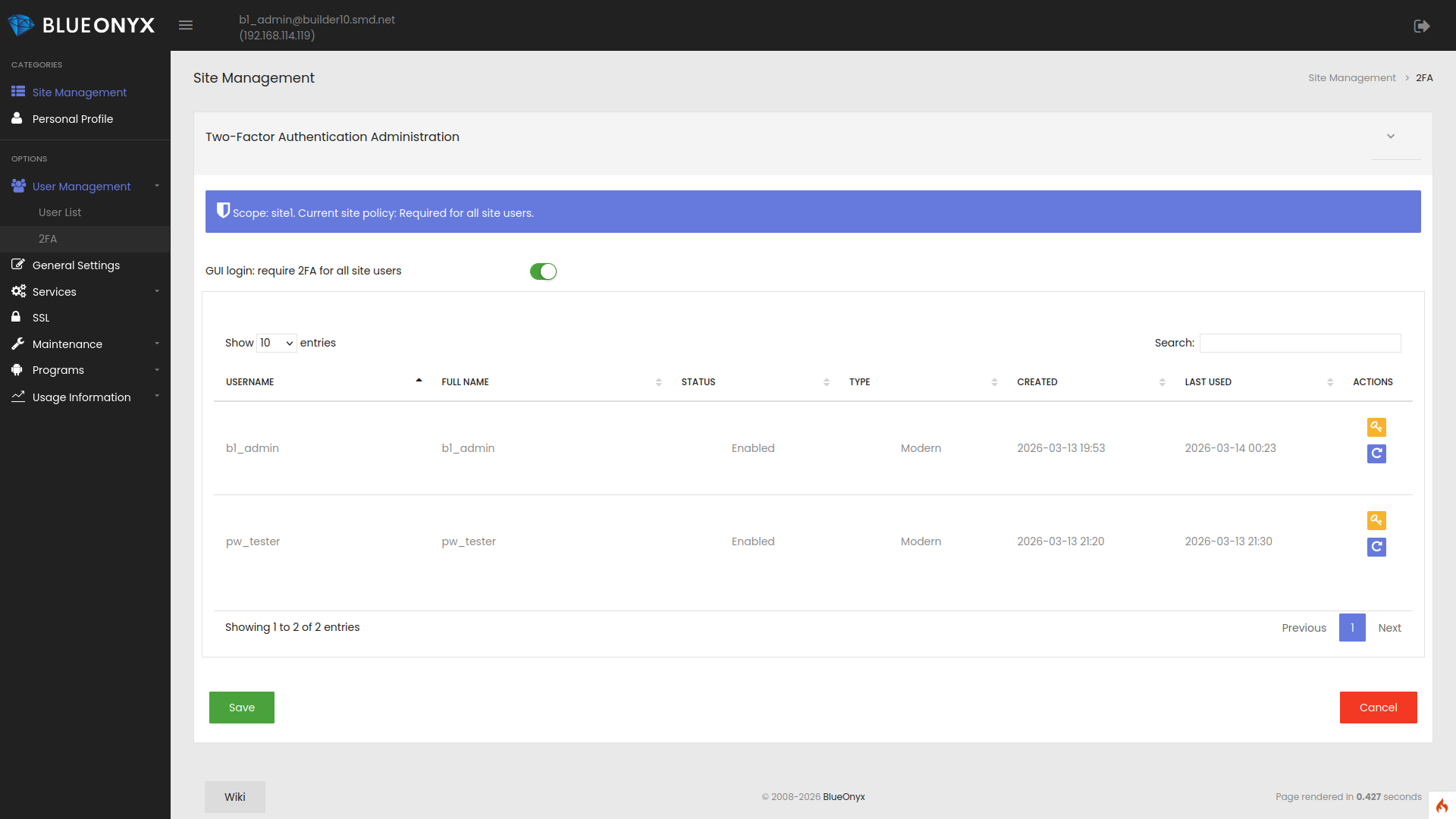
Site administrators can manage it at Vsite level:
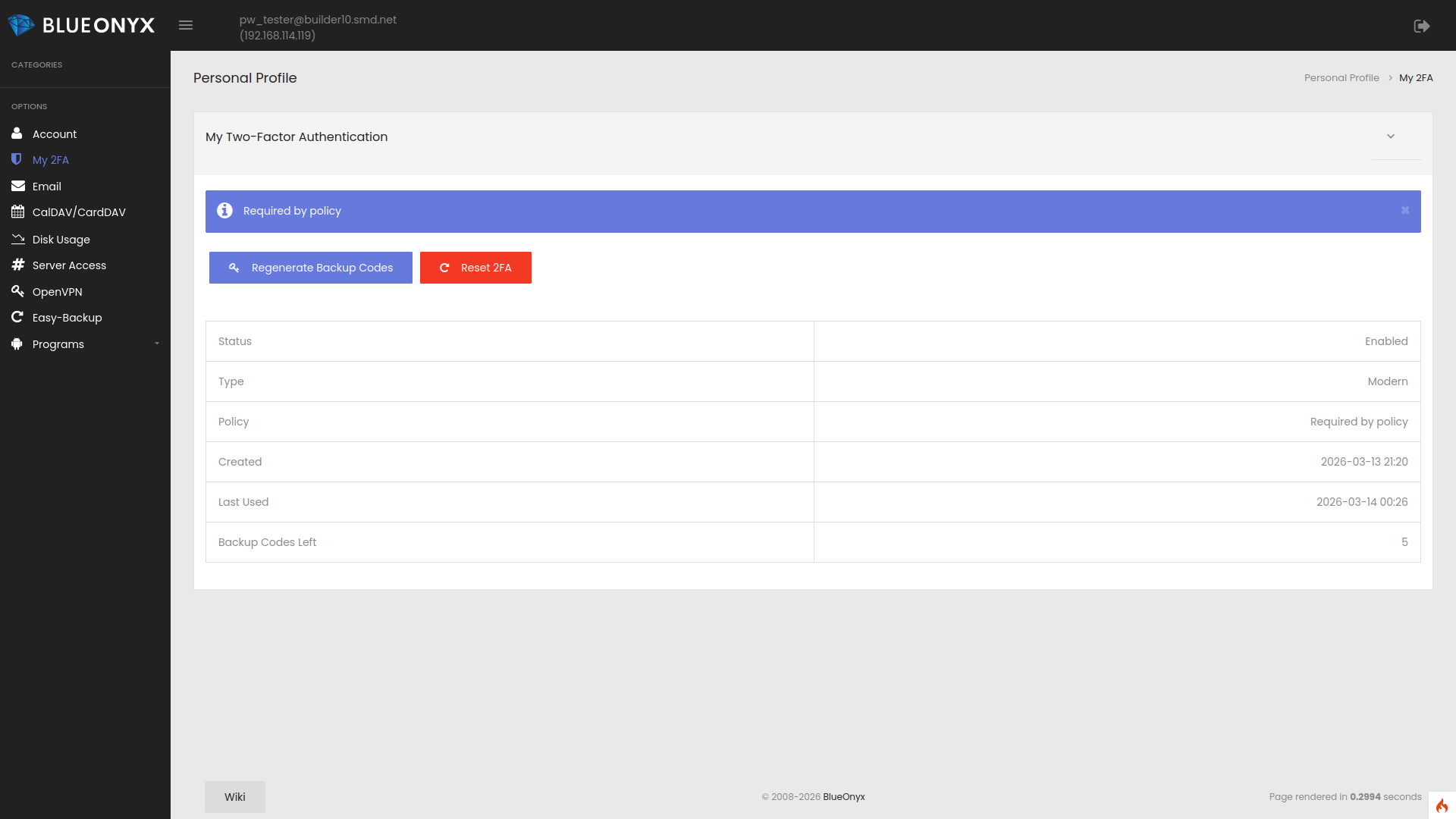
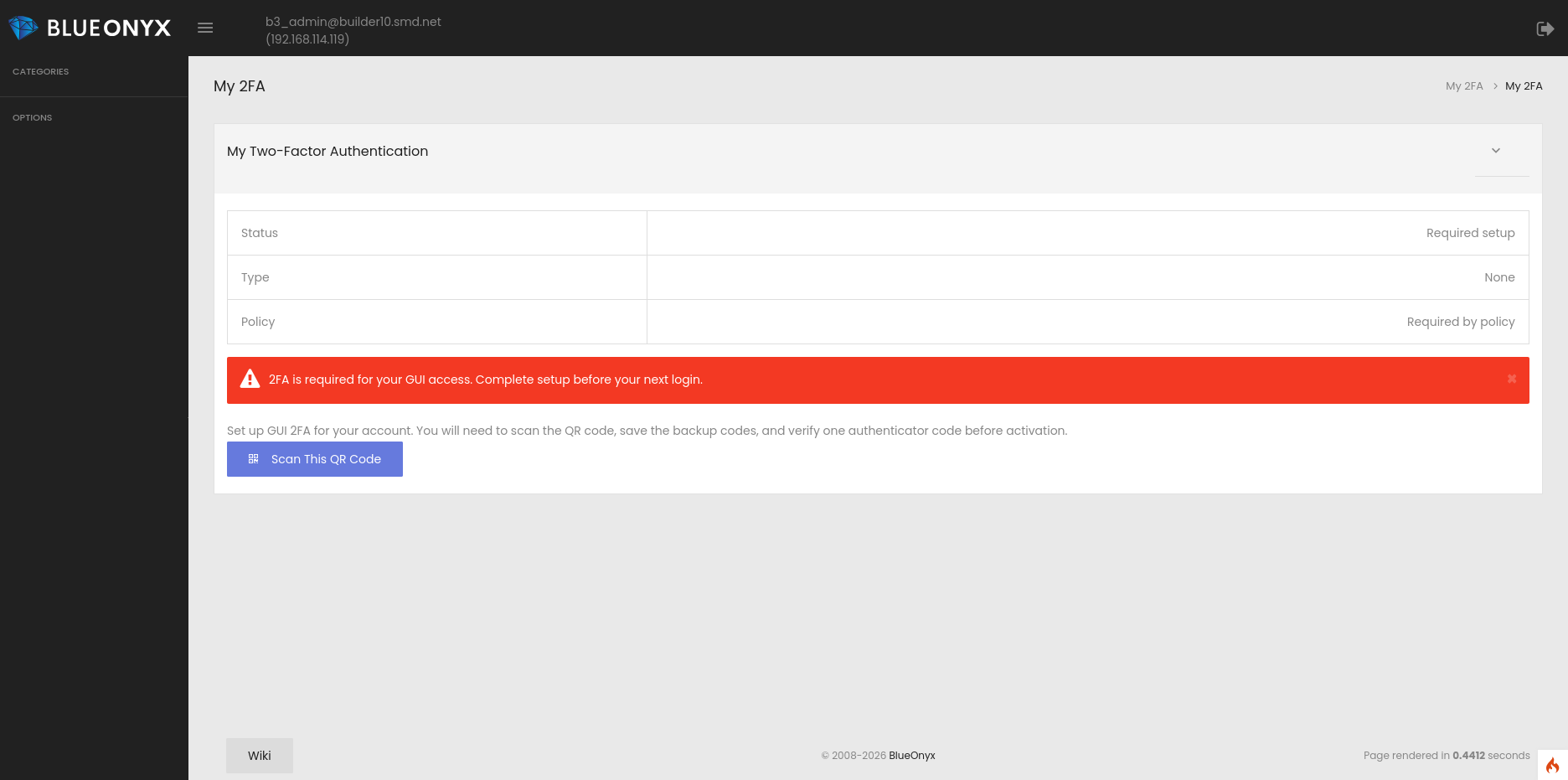
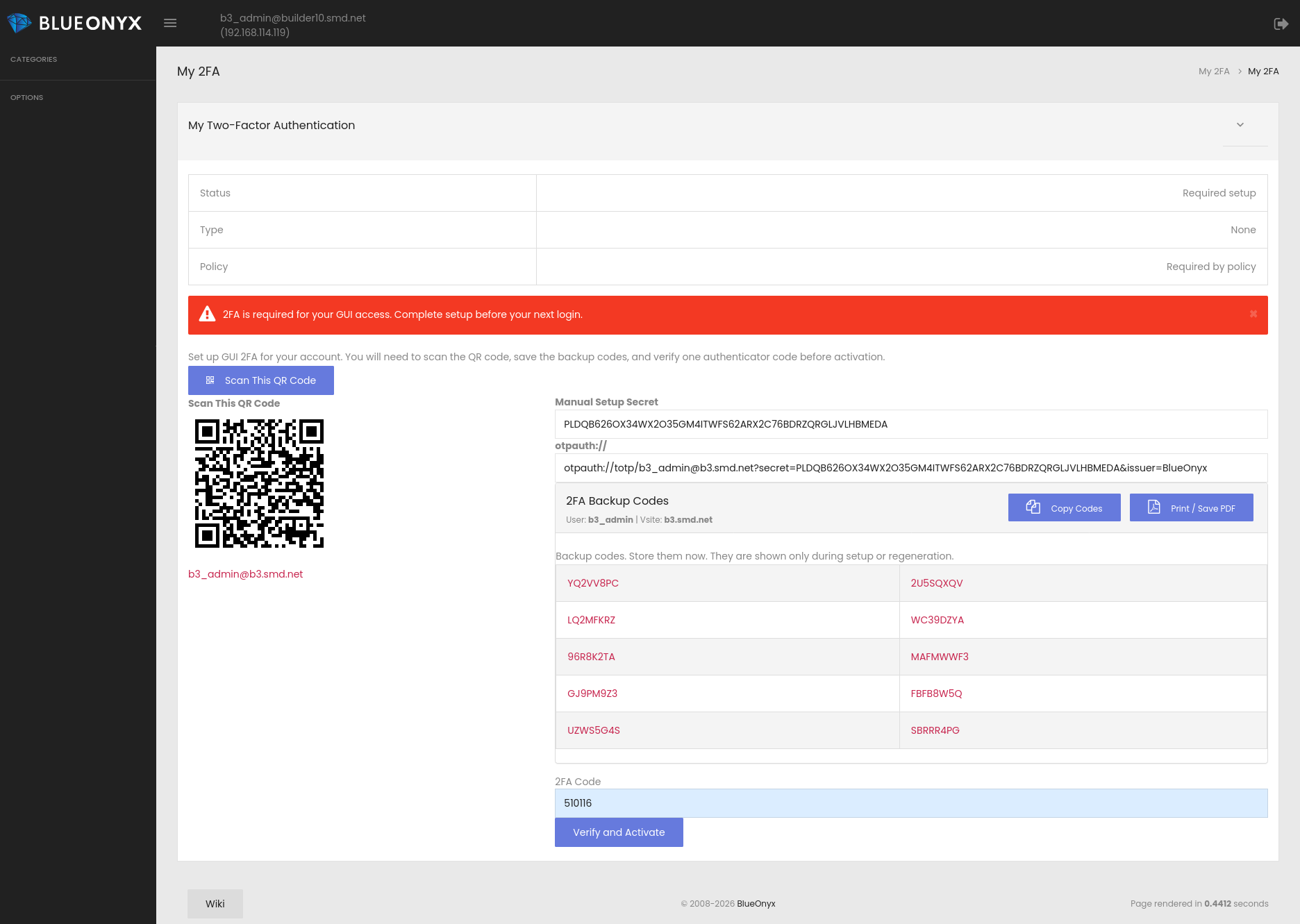
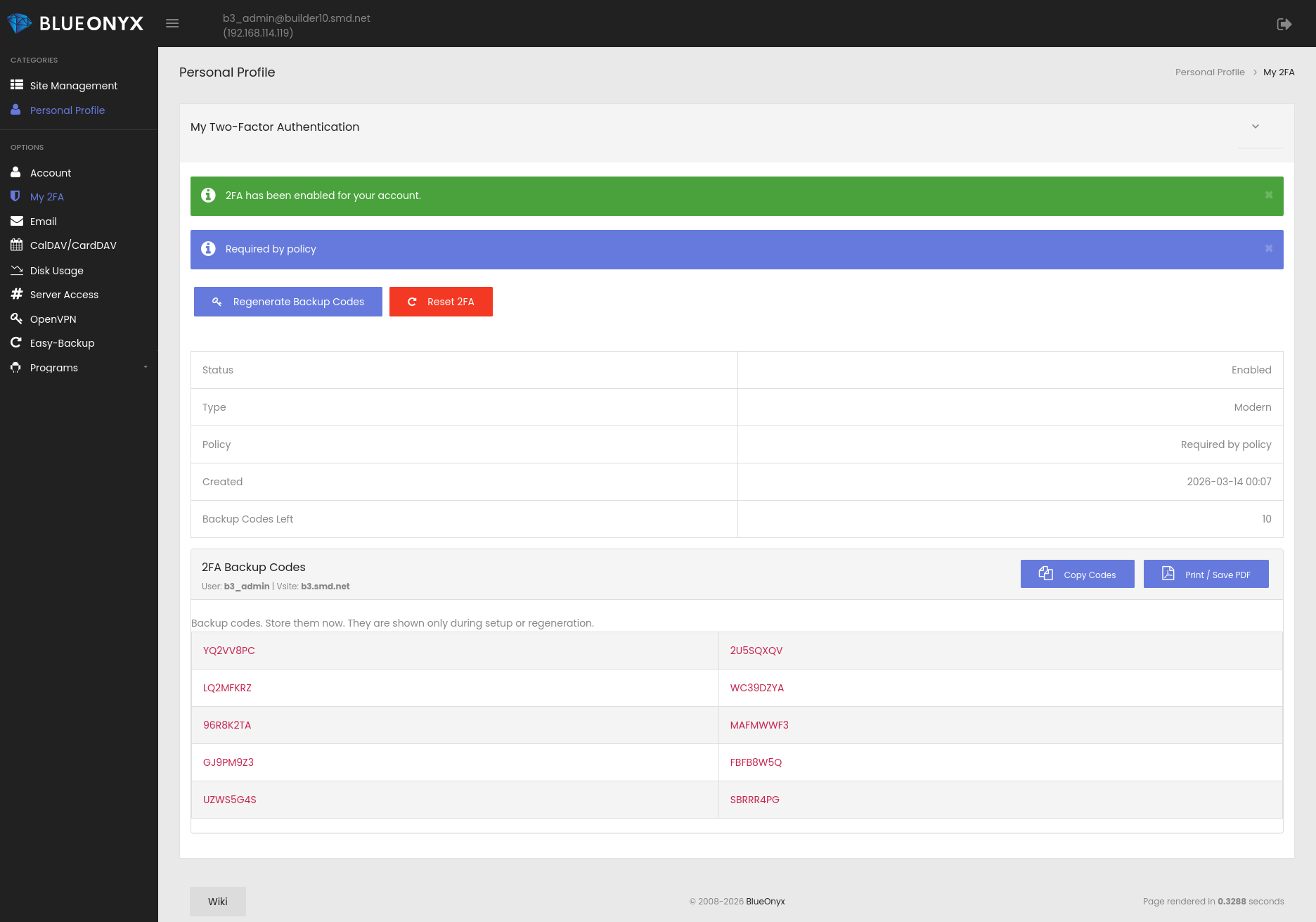
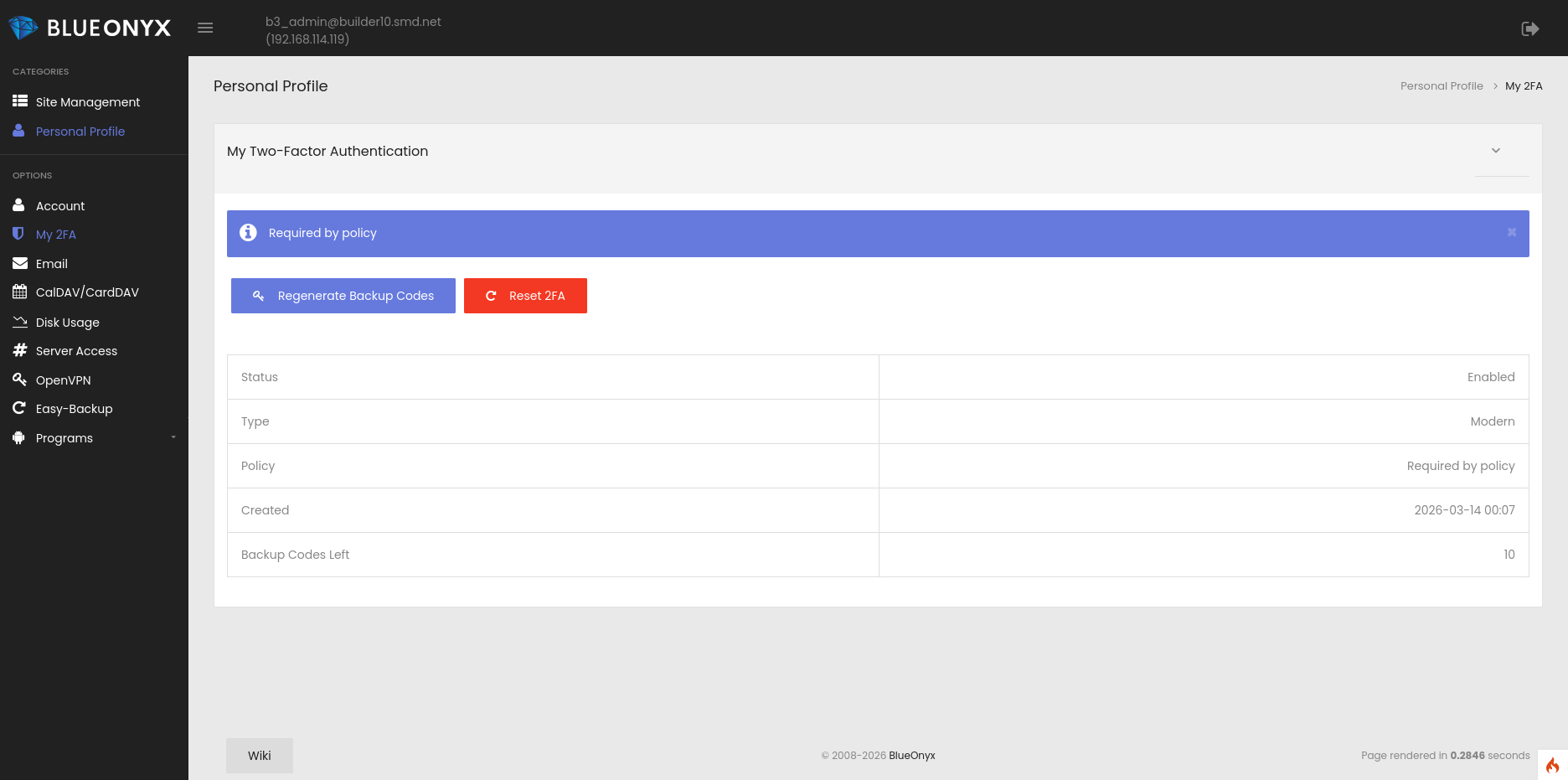
And users have a dedicated self-service page to configure and manage their own 2FA.
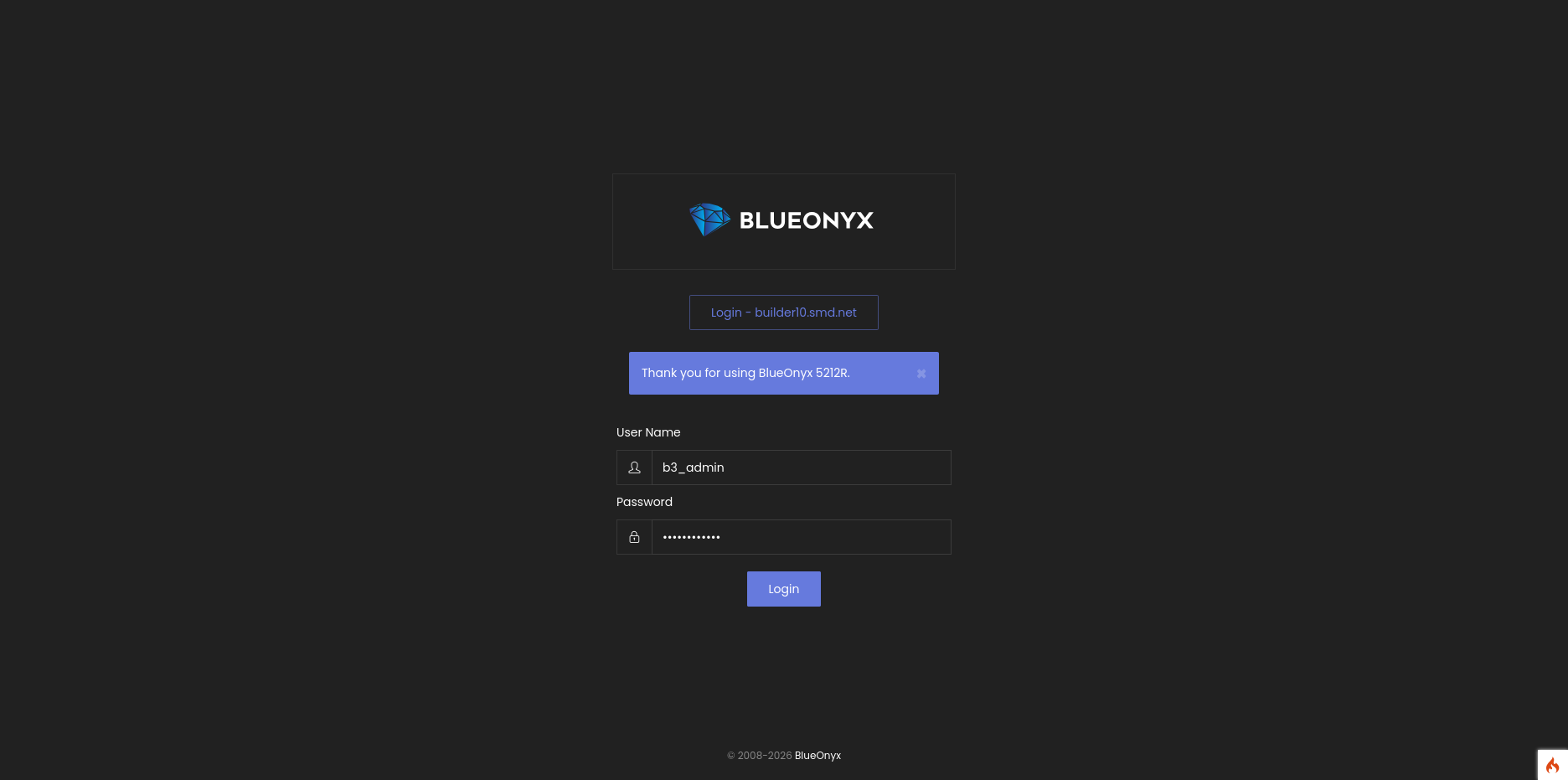
One important improvement is that accounts which are required to use 2FA can no longer postpone setup indefinitely. If 2FA is mandatory for a user and has not yet been configured, BlueOnyx now redirects that user straight into the setup process and restricts GUI access until enrollment is completed successfully.
This helps ensure that security policy is not only defined, but actually enforced.
The user experience has also been improved. The personal 2FA page now presents setup information more clearly, including QR code enrollment, backup codes, and status information in a compact and easier-to-understand format. Compatibility with authenticator tools such as 1Password has also been improved.
For environments with existing legacy Google Authenticator-based setups, backward compatibility has been retained. Legacy users can still log in, and their 2FA data is migrated automatically into the newer storage model after successful authentication. This allows administrators to modernize deployments without disrupting existing users.
In addition, GUI 2FA and password-based SSH OTP handling are now aligned more closely, reducing duplicate configuration paths and making 2FA behavior more consistent across the platform.
Overall, these changes make BlueOnyx 2FA easier to manage, easier to use, and much harder to bypass.
Release date:
The updated 2FA implementation is currently in testing and evaluation on a BlueOnyx 5212R development server. The changed code is in SVN and is currently undergoing a thorough review prior to merging it into the baseline code base. A tentative release date of 18th of March has been set, but the actual release could be a bit sooner or later depending on how well testing and backporting to BlueOnyx 5211R and 5212R go.