Security Update: 5207R, 5208R, 5209R, 5210R
A potential security flaw was found in the module base-email. YUM updates are available.
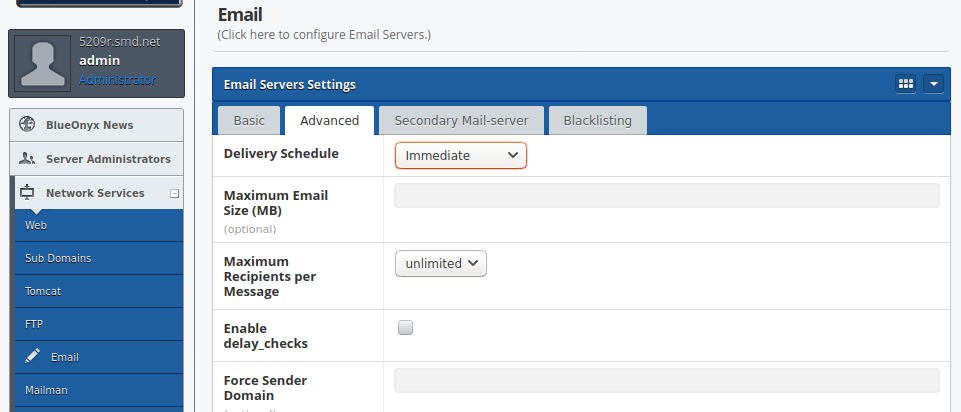
A potential security flaw that affects non-standard configurations of BlueOnyx (all versions) was found today in the module base-email. If the MTA was Sendmail and the "Delivery Schedule" was NOT set to the default value of "Immediate" in the GUI (as shown below), then a sender of emails was potentially able to bypass SMTP-Auth as well as certain access restrictions. This might have allowed unauthenticated relaying of emails through affected BlueOnyx servers.
However, BlueOnyx 5210R ships with Postfix as default MTA (not affected) and all versions of BlueOnyx have the default "Delivery Schedule" set to "Immediate" (which is safe). But if you manually had changed the "Delivery Schedule" to anything else but "Immediate", then BlueOnyx servers with Sendmail running were affected by this issue. The presence of the AV-SPAM and an enabled Milter-Greylist had the side effect of preventing the issue, though.
Permanent mitigation: YUM updates have been released today (2020-09-06) which fix the problem. These updates remove all "Delivery Schedules" but the safe "Immediate" from the GUI and revert any affected server back to a safe Sendmail configuration.
Many thanks to Rodrigo Ordonez from xnet.com.mx for reporting the issue!